Every 39 seconds one hacking attack takes place. In general, hacking is defined as an act of intruding into a network or computer. And the hacker represents an individual or a group that tries to execute the hack. What started as an experiment in the laboratories of MIT in the 1960s has turned into a big threat. According to website hosting provider Hosting Tribunal, the average number of records stolen by different types of hackers has reached 75 records per second. And the intent is generally not good.
Hackers work alone or as groups in the dark web to disrupt standard operations. They are capable of penetrating secure government networks, enterprise networks, and even a daily internet user’s network.
The goal of hacking attacks may vary. Sometimes a hack is conducted to get control of a network, and sometimes sensitive information is stolen. At any rate, the victim is at risk.
Here is the video that demonstrates how powerful hackers have become:
How to Beat Hackers at Their Own Game?
To keep their guard up and prevent any potential losses, organizations started working with various types of hackers. Initially, the hackers were paid to identify a network vulnerability and then the internal IT team would fix the soft spot. As the volume and scale of attacks soared, organizations felt a pressing need to have an in-house team of different types of hackers in cybersecurity. And that is how a new league of hackers with varied skill sets evolved. As per the experts, the ethical hacking industry will boom into a $101 Billion Opportunity for young talent by 2020.
Is There a Role for You?
Let us look at the varied types of hackers that exist today and how the ecosystem will generate 1.5 million job opportunities:
What are the Different Types of Hackers? Especially, What are the 3 Types of Hackers?
Black Hat Hacker
In simple words, these represent the bad elements of the cyberspace and operate the dark web. Over time, different types of hackers with malicious intent have turned cybercrime into a $405 billion industry. They design programs and algorithms that penetrate networks and steal sensitive information. This sensitive data is then put on sale on the dark web. In the Equifax hack of 2017, identity details of millions of US citizens were stolen and floated across on the dark web. Such malicious attacks are conducted by black hat hackers. They try their best to protect their own identity as the attacks they tailor are criminal.

The identity or financial data is being especially exploited by the black hat hackers. When we talk about what are the three types of hackers, black hat hackers are the primary ones with bad intent.
Suicide Hackers
As the name suggests, he is the type of hacker who executes a hack solely for destruction. And in the process, he may not care if his identity gets revealed. They execute a hack either to take revenge, extract money or become famous. Whatever be the intent, such types of hackers constitute an enormous threat.
Grey Hat Hacker
Someone who does not intend to exploit the vulnerability of a network or a computer system for his gains. Such hackers pursue hacking as a passion or try to break into systems for the public good.
These hackers do not have the right to penetrate a network. But once they do, they let the owner of that network know and might receive some remuneration in return. These rank third when we try to find an answer for “What are the three types of hackers”?
White Hat Hacker
A hacker who has the authority to intrude networks or computers. To put it concisely, he is the one who works ethically with an organization to identify the vulnerabilities from where the black hat hackers can penetrate the system. When the cybersecurity experts were asked what are the 3 types of hackers, Whitehat hackers were identified as a major category.
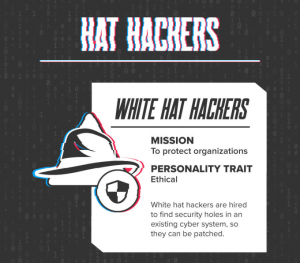
They consistently try to develop algorithms that can be used to break into a system. Working from a black hat hackers mindset, they keep up-to-date with the various types of hack going around. And ensure the network they are protecting is immune to evolving attacks.
Enterprises, government bodies, and even small-scale organizations have realized the need for ethical hackers in their team. And that is why multiple job roles around it have cropped up in the industry.

Script Kiddies
An amateur hacker is known as a Script Kiddie. He may not necessarily be able to program an attack, but he has access to the internet from where he can download malicious programs. They might even purchase such programs from the dark web and try to execute a hack without any goals. Most of the times they barely recognize the impact of the hack. In spite of their lack of experience, Script Kiddies can do potential damage to the victim. Some of the types of attacks Script Kiddies execute are developing a fraudulent website and collecting user id and credentials.
Hacktivist
The term was coined in 1994 when a group of politically aware hackers tried to penetrate networks. Such types of hackers try to cause a stir by spreading a particular ideology. They might use common tools and techniques like DDoS or Doxing to deface a website. Hacktivism is defined as a hacking attack to bring in political or social change. But there may be some who are there for personal gains.
Red Hat Hacker
He is the savior of the cyber world, as a red hat hacker directs all of its attacks towards black hat hackers. They plan their attack in such a way that the black hat hacker’s infrastructure is threatened. They operate on similar lines as the White Hat hackers but might be completely brutal in the way they operate.

That’s because unlike White Hat hackers, they don’t merely stop the attack but also try to destroy the black hat hacker.
Blue hat Hacker
These are the types of hackers who are invited by an organization to test a network or system before its launch. They do not possess a very refined skill set so are just like Script Kiddies. The Blue Hat hackers are not employed by an organization and always work like outsiders trying to penetrate the network.
Green Hat Hacker
Someone who has only just started to learn hacking is known as a green hat hacker. They do not pose a threat to the cyber world. He is predominantly seen participating in hacking forums and communities trying to learn from the skilled and more experienced ones.
Social Media Hacker
He is one who possesses very limited programming language. But his intent is mostly malicious as he intends to steal the user data. Some of the Script Kiddies also conduct social media account hacks to get hold of sensitive user data.
What are the Roles and Responsibilities of the Various Types of Hackers?
Ethical Hackers are required to work as per the guidelines of the organizations they are employed by. They are required to work ethically to protect the network against all types of attacks.
These types of hackers in cybersecurity are required to know the networks, security aspects, programming, and hacking methodologies efficiently. As they are also required to code the algorithms, they must possess absolute knowledge of the Software Development Life Cycle. Some of the crucial skills they must possess are:
Network Understanding
For an ethical hacker understanding the networks is critically important. That is because the black hat hacker constantly tries to target the vulnerabilities in the network itself.
Scripting Skills
As the networks are typically written in some type of scripting language, diverse types of hackers, especially the ethical ones must possess scripting knowledge.
Knowledge of Databases
Databases remain the primary areas where black hat hackers attack the system. The ethical hackers and all types of hackers in cybersecurity must possess knowledge of SQL DB2 and more.
Platforms and Tools
The ethical hackers must have extensive knowledge of Windows, Linux, Unix and a variety of hacking tools. To execute a hack, some standard tools and techniques are used by different types of hackers. Here is a list of some immensely popular tools and techniques.

Common Hacking Tools and Techniques
Keyloggers
It is a program specially designed to record all the keystrokes received by the system. Sporadically a dedicated keylogging device is used to log the strokes and sometimes a malicious program is forced into the computer system. A Keylogger primarily captures any type of data keyed in by the user. It may be something like user id, password, mobile number, credit card details or any type of sensitive data.
Rootkits
A rootkit is principally a group of programs like keyloggers, bots for executing DDoS attacks or more. It is malicious software downloaded on the system or network that gives remote access to the hacker. Using this, the hacker can gain constant access to the restricted areas of the networks. When experts were asked about what the choicest tools of the different hackers are, rootkits ranked on top.
Rootkits constitute a serious threat to a network because they cannot be detected even by the antivirus programs. They are employed to execute stealth attacks, backdoor access, and DDoS attacks. The ethical hackers and types of hackers in cybersecurity use rootkits to detect attacks, emulate software, enforce digital rights management and device anti-theft protection. Some of the frequently used rootkits are:
User-mode rootkits
Kernel-mode rootkits
bootkits
hypervisor rootkits
firmware rootkits
Vulnerability Identifier
A program specifically designed to identify the weakness of a system or network. According to recent reports, almost 20% of the bot traffic witnessed today is a vulnerability scanner. The White Hat hackers and various types of hackers use these scanners to identify weak spots. These are an ideal choice because they do not discriminate between different pages, different nodes or systems. They keep on attacking aggressively trying to find a penetration point.
Hacking Techniques
Multiple hacking techniques are being used by both black and white hat hackers. Some of the most common ones are:
Distributed Denial-of-Service (DDoS)
An attack by a malicious source to intervene in the average traffic directed towards a website or a server. Generally, a DDoS attack floods a lot of traffic towards a server impacting its performance for the non-malicious users. Most of the time the server crashes or the website stops responding to normal requests.
The attacker gains control of the network or server and attacks at distinct layers. Some of the layers attacked are the physical layer, data link layer, network layer, transport layer, session layer, presentation layer, and application layer.
SQL Injection Attack

A web application always uses a database in the backend and the SQL injection attack is directed towards the database. Vulnerable user inputs are identified on a web interface and using these inputs malicious SQL statements are directed towards the database of the setup. Different types of hackers try to procure sensitive information from databases like user ids, passwords, identity data and more.
What are the Responsibilities of an Ethical Hacker?
To work ethically, a hacker must try to intrude on a network or system with prior authorization. He has to be a part of the security team and must never use sensitive data or soft spots for his benefit.
Before the ethical hacker executes his hack, he must inform the organization about his plans and methodologies. In case any vulnerabilities are identified, he must report them to the security heads and work with the team to fix the patches. Maintaining the confidentiality of such data vulnerabilities is tremendously important. An ethical hacker must ensure he leads no trails of his hacks for malicious types of hackers in cybersecurity into the system.
Conclusion
Apart from an ethical hacker, various types of hackers help to keep cyberspace secure. As we explained most of the hackers that co-exist, it is noteworthy that ethical hackers enjoy ample opportunities to work with enterprises across the globe. The US alone assigned a budget of $14.98 billion in 2019 to combat hacking attacks. All major giants and government bodies have started expanding their cybersecurity teams to keep their networks, and databases secure.
Every day hackers identify a new vulnerability every day so the experts need to be on top of everything and know what is cybersecurity & also should follow cybersecurity tutorials to ensure the internet remains a safe place.
Are you also inspired by the opportunity provided by Cyber Security and are looking forward to building a career in it? Enroll in Digital Vidya’s Cyber Security Course to become a Cyber Security Expert.