Are you an aspiring ethical hacker and want to learn about the different types of hacking?
This post covers all the types of hacking along with the ways to prevent them.
Ian Murphy, Kevin Mitnick, Johan Helsinguis and Robert Morris.
Do these names ring a bell in your mind?
Here is the rub, these are the masterminds behind some of the biggest computer hacks ever.
Ian Murphy aka “Captain Zip” is notorious for being the first convicted unethical hacker after he hacked AT&T’s network of computers and altered the internal clocks to meter billing rates.
Right from these small tweaks to massive exploits, the different types of hacking have shaken up the internet, enterprises, public networks and more over time.
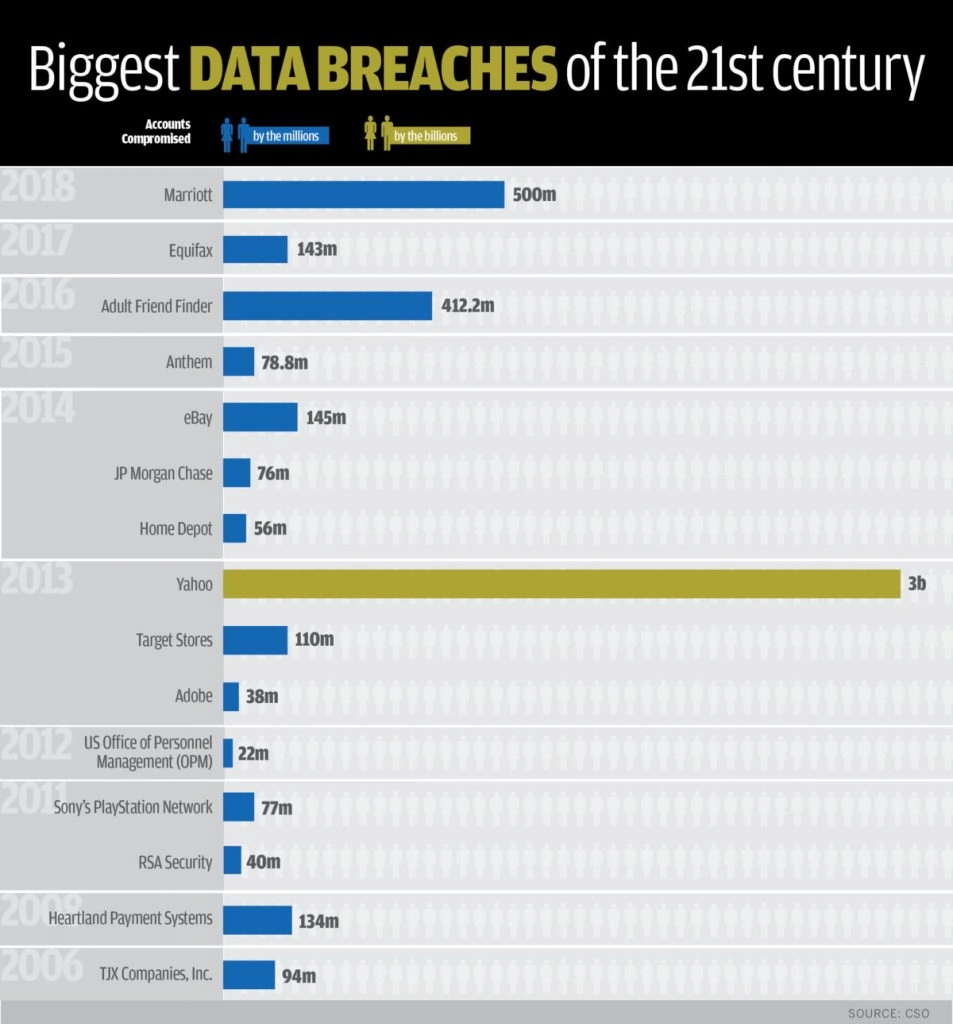
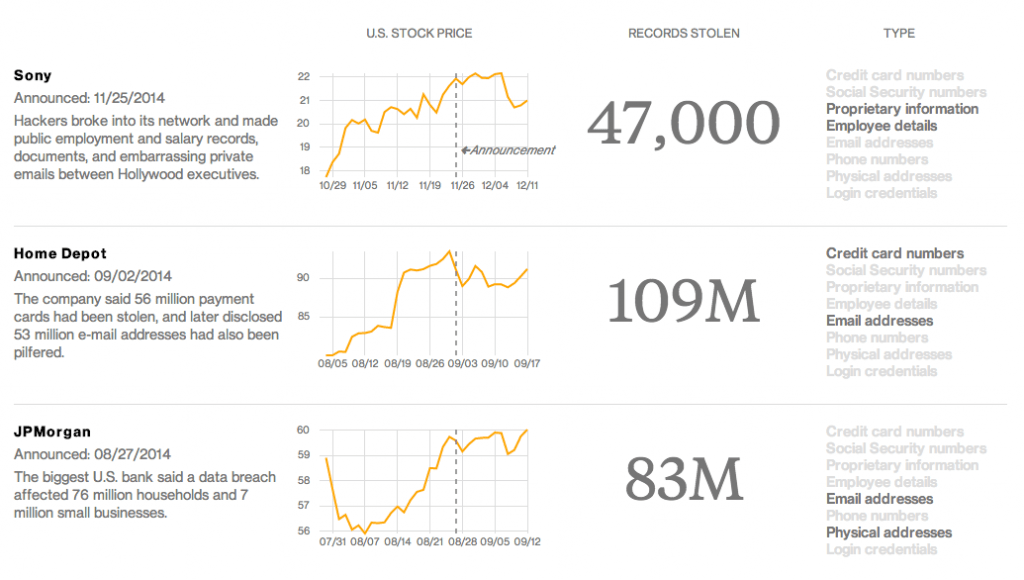
No one has been speared- Sony, Adobe, Target, Equifax, Yahoo, Marriot, eBay, JP Morgan Chase, LinkedIn and an endless list of small and big players have been at the receiving end.
The term “hacker” was coined in MIT’s AI Labs in the 1960s and by 1970s the types of hacking attacks were already going out of control.
Overall these years the hacking techniques have gotten more sophisticated and targeted. Hacking continued to be a major contributor to data breaches in 2018 when it accounted for 57.1 per cent of breach incidents.
Threats continue to get bigger!
To understand how what is hacking and how different types of hacking have evolved let us look at it from the point of inception till today when it has become dangerous.
Different Types of Hacking over the Years
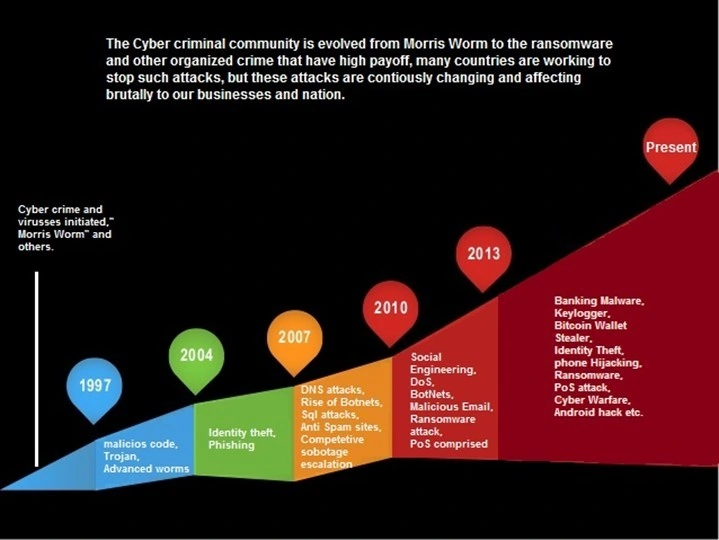
Early Hacking (the 1960s–1970s)
All because the term was coined in the 1960s, we consider it to be the decade of inception of hacking. But the fact is that timeline of computer security hacker history states some noteworthy events right from 1903 when inventor Nevil Maskelyne disrupted public usage of Marconi’s wireless telegraphy technology.
He sent insulting Morse code messages by overriding the projector in the auditorium.
The hacking took an actual shape in the 1960s when the computer programmers tried to hack systems to make sure they performed better.
The ones who made it turned against it and led to one of the worst types of hacking attacks of that time when AT&T’s long-distance switching system operations were overridden with high-pitch whistles to make free phone calls.
The impact was so massive that the FBI has to intervene and crack down the hacker network.
It was 1979 when Kevin Mitnick broke into his Ark computer system of Digital Equipment Corporation.
Middle Age of Hacking (1980s)
With the introduction of Personal Computers by IBM, every place was at the receiving end of a hacker attack. Starting from 1 million computer units in 1980 to 30 million in 1986, the personal computers and the networks they were using opened up new hack breed grounds for malicious attackers.
The peak of seriousness was reached.
The Great Hacker War was declared by the hacker groups Legion of Doom (LOD) and Masters of Deception (MOD). Both the groups were working as rivals by trespassing into private computers and computer networks, jamming phone lines and monitoring calls illegally.
After the intervention of the Federal Bureau of Investigation, some arrests were made and the groups dissolved and commoners got to know what is hacking.
Hacking Rides the Internet Wave (the 1990s)
This is the era when the hackers turned sophisticated and adapted to the World Wide Web. The simple types of hacking programs changed from BBS to hacking web sites.
It started as a joke by some computer programming junkies and has evolved into a $2 Trillion industry. Every computer and computer network is a threat of attacks like Denial-of-Service (DoS), Distributed Denial-of-service (DDoS), Man-in-the-middle (MitM), phishing and spear-phishing attack, Drive-by and password attack, SQL Injection attacks, Cross-site scripting (XSS) and more.
Hacking attacks that have been altering websites of United States Department of Justice, CIA, U.S. Air Force, Nuclear program systems, Credit card websites, and every possible digital interaction raise a question what is hacking and how much potential harm can it do.
Types of Hacking Techniques that you may Encounter in 2019
Every personal information has turned digital and our digital footprints have increased excessively. Unethical hackers are trying different types of hacking techniques to get hold of data or computer systems to cause the intended damage.
Here is an insightful video for type of hacking:
Denial of Service (DoS\DDoS)
GitHub the developer platform for open-source coding was taken down with massive traffic of 1.35 terabits per second in 2018. It was the record-breaking traffic it had ever received and the platform was not prepared to handle it.
Thus a Denial of Service (DoS) targets to flood a website or a network server with traffic much more than it can handle this leading to a crash.
The actual users start facing denial of services and this is the most common types of the hacking technique employed.
While the network owners remain occupied with solving the traffic issues, a small piece of malware is sneaked in sometimes which takes some days to be discovered till then potential damage is done.
Botnets are being designed to automate the attack that sends multiple requests, packages or messages which is overwhelming for the system.
A couple of years back the DDoS or Distributed DoS attacks were very unsophisticated but over years the DDoS toolkits have become capable of launching both infrastructure and application-based attacks. It has been noted that the application-layer DDoS attacks are highly targeted.
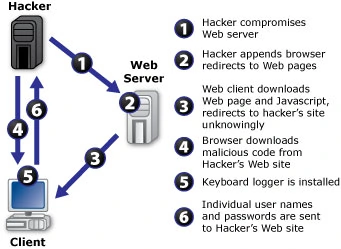
Keylogger
A Keystroke logger or system monitor is a software used for surveillance and records the keystrokes a user makes on the keyboard or a touchpad. The keystrokes are then retrieved to generate the user’s login ID and passwords without his knowledge.
The Keylogger can be a software or hardware which is used to steal personally identifiable information (PII). Anti-keylogging software’s can be used to detect the introduction of a Keylogger program or hardware. Banking sector and other financial institutions are at major risk of attacks from Keyloggers.
Public WiFi Fake WAP
A common public WiFi user falls victim to the Fake WAP attack at a local coffee shop, the airport, and shopping centres. A fake wireless access point is created by the hacker which is then connected to the free official WAP.
It is the simplest possible type of hacking attack, as a hacker is just required to download a simple software or what we know the “Hot Spot” feature of the mobile to create a fake WAP.
The problem begins when the hackers start using a tool dedicated to sniffing data once the user connects to these fake WAPs.
Using the Fake WAP, a hacker tries to either steal your login credentials or simulate a Man-in-the-middle attack like Ettercap that sniffs live connections or Metasploit Project using which the hacker takes complete control of the WAP user’s device.

Waterhole Attacks
Using a waterhole attack types of hacking technique the hacker targets to attack a specific group of internet users. This is accomplished by identifying the website which is mostly visited by the group.
The website is infected with a virus, worm, malware or malvertisements that allows a hacker access to the user’s computer system once the website is launched by the user.
It is clickbait kind of attack where popular niche websites are targeted to attack the website visitors. These are pivot attacks whereby infecting a legitimate website, the computer systems or devices of the target audience are infected.
These kinds of attacks are conducted in large enterprises, on banking websites, government websites, at public places by setting fake WAP and other ways.
The hacker is on a continuous watch for the popular website with vulnerabilities. These websites are injected with malicious code which redirects the website visitor to a website that has a malware waiting to infect the systems.
Waterhole attacks are targeted on organizations where the employees, vendors or any kind of website user uses less secure wireless networks to gain access.
Although these attacks are not very popular they remain undetected for a long time.

Passive Attacks
Very commonly known as an eavesdropping attack, a passive attack involves types of hacking where the hacker just listens and monitors the information that is being passed. In no way does a hacker try to change any user data or system settings. It is a kind of spying activities.
What is the hacking of this kind? From a simpler perspective, it is the exact opposite of an active attack, where the hacker tries to get into the system by introducing malware and then altering the data.
While the passive attack may not seem to be a big threat as compared to active attack, the damage can be substantial if there the hacker lays hands-on details like your banking user id and password.
Many a time’s government bodies or high-end security organizations use passive attacks for non-malicious intents.
But it has been noted that the active attacks are made more targeted by collecting information using a passive attack where the user hardly gets to know that his information and data is being used to build a targeted attack.
Different types of hacking that are more advanced
Whenever a criminal tries to hack a network, he tries to use the most common types of hacking techniques that have proved to be effective time and again.
He simply tries not to re-invent the wheel and just tries to tweak the existing techniques and carry out more sophisticated attacks. The cybersecurity attacks that make headlines today are generally one of the following attacks:
Phishing
Phishing has been accountable for 90% of the data breaches and the number of phishing attacks has grown up by 65% in 2018 only.
The worst aspect of Phishing attacks is they are evolving rapidly. Every month 1.5 million new phishing sites are being identified.
By acting as a legitimate source, the hackers employ social engineering and different types of hacking techniques to lure victims to perform an action that could range from clicking a link or downloading an attachment that has a malicious link. Email is the most popular channel to conduct phishing attacks.
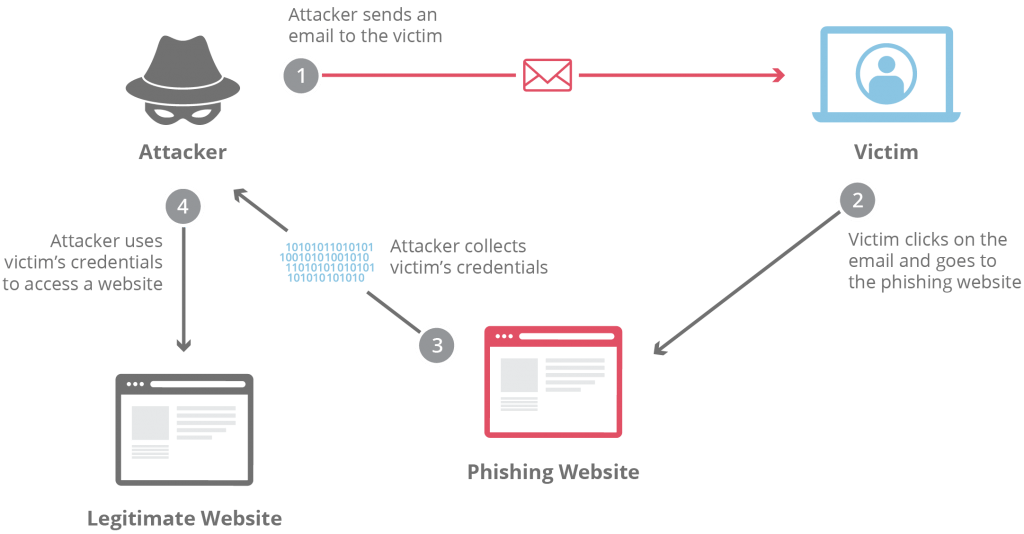
Some specific types of phishing attacks that are very targeted and used most commonly are:
Spear Fishing
A well-planned attacked where the information about the targeted audience is collected and studied so that the success rate is higher. Disguised as a legitimate source, spear-phishing email is no random message that can be doubted.
These are created in such a manner that the victims trust them and cause a knee-jerking reaction. Most of the times these attacks are conducted during the holiday season when the email traffic is very high and in the urgency of catching a deal, victims get lured.
Once the victim clicks a malicious link, he uses his user-id and password to log in, this is the moment the hacker was looking for. Thus spear phishing can prove to be very dangerous.
Whaling
The Whaling attacks target the mailboxes of the executives of a specific organization. CEOs and CFOs are the most targeted ones.
As this senior position always have access to business-sensitive information, attacking them proves to be more beneficial to the hackers. These are among the highly targeted attacks.
Individuals and Organizations all are at risk
Virus, Trojan, Worms
The software programs that enter the victim’s system or network and keep monitoring or altering the data and information being transmitted.
The Virus or trojans are malicious and can sniff the user data or encrypt the user files asking a ransom to share the decryption key.
Viruses, Worms, Trojans, and Bots have a different way of infecting the computer system but the impact depends upon the kind of sophistication it is built with.
Cookie Theft
The cookie theft revolves around mimicking a victim’s cookie over the same network. By using these cookies, a hacker can access websites that were already visited by the victims and malicious attacks can be conducted.
Cookie theft occurs when a hacker gets access to the unencrypted session data which is being used to act like the real user. A user is susceptible to Cookie thefts when he browsers trusted sites over public networks.
Conclusion
Hacking is leading to computer frauds where the hackers try to gain access to personal user information. The information can range from email address to phone numbers, from user Ids to passwords and even identity thefts.
By gaining access to the information at a personal level, the hackers try to gain unauthorized access to bank accounts, social media accounts and more to magnify the damage.
If you are an aspiring ethical hacker, grab the opportunity to start your career in Ethical Hacking, here is a list of top Ethical Hacking Interview Questions that will help you to crack your next interview.
If not the direct user id/password route, the hacker tries to encrypt files, push malware and ransomware to extort money from the victims.
Evolution of the internet has been a game of good, bad and ugly and “hacking” is the ugly part of the game.
If you also want to become a cyber security professional, take up the cyber security course and take your career to the next level.